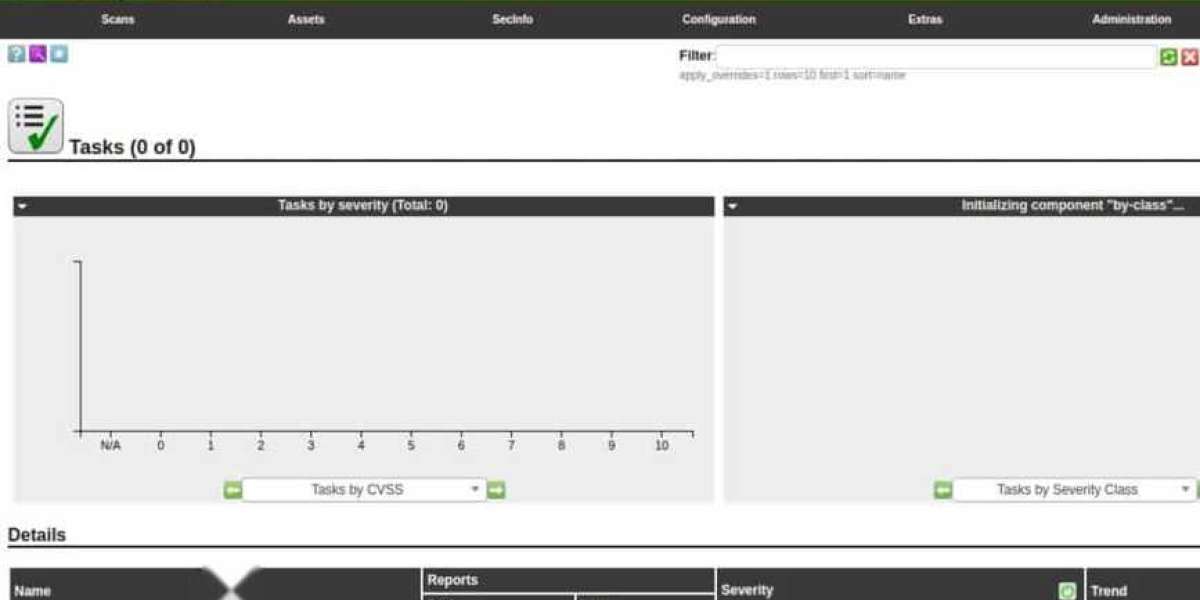
Network Security Auditing Solutions
Comprehensive Tools for Network Security Auditing
Network security auditing plays a crucial role in modern enterprise cybersecurity strategies. By thoroughly examining IT assets and policies, organizations can identify vulnerabilities before they become exploitable threats.
Why Network Security Audits Matter
Effective security audits provide a comprehensive overview of your network infrastructure, helping troubleshoot specific issues while assessing your organization's resilience against known security threats.
Top Security Auditing Solutions
Cloud-Based Options
N-able N-sight delivers robust remote monitoring with specialized attack surface scanning capabilities, making it ideal for managed service providers protecting client networks.
Intruder offers flexibility with scheduled monthly scans, on-demand vulnerability assessments, and professional penetration testing services.
Site24x7 Network Configuration Manager secures network device settings through its cloud platform of monitoring and management tools.
Trellix XDR Platform aggregates activity data from multiple sources including endpoints and networks for comprehensive threat detection.
On-Premises Solutions
ManageEngine Vulnerability Manager Plus performs systematic security checks across your network, compatible with Windows and Windows Server environments.
ManageEngine Log360 functions as a SIEM solution, collecting and storing logs from network endpoints and cloud platforms for compliance auditing.
Netwrix Auditor provides configuration monitoring with automated alerts and API integration capabilities.
Tools for Service Providers
Atera offers a comprehensive SaaS platform with remote monitoring, management systems, and audit report generation.
Kaseya VSA includes IT asset discovery, customizable dashboards, reporting, and automation features.
Free and Open-Source Options
Nessus provides free vulnerability assessment with extensive configuration templates and customizable reporting options.
Nmap serves as an essential port scanner and network mapper, available through command-line or graphical interface.
OpenVAS delivers vulnerability assessment specifically designed for Linux environments with regular security updates.
Spiceworks Inventory offers free web-based IT asset management with automatic device discovery.
Specialized Testing Tools
Acunetix focuses on web application security, detecting thousands of network vulnerabilities when integrated with OpenVAS.
Network Inventory Advisor provides cross-platform inventory scanning compatible with Windows, Mac OS, and Linux.
Metasploit enables comprehensive penetration testing by identifying exploitable vulnerabilities in your network infrastructure.
Selection Criteria
When evaluating these tools, consider whether they offer:
- Automated vulnerability assessment
- Penetration testing capabilities
- Compliance-oriented activity logging
- Asset discovery and inventory management
- Configuration and logfile protection
- Integration with patch management systems
- Free trial availability or free tier options
- Overall value proposition
N-Sight from N-able offers comprehensive network security management through its cloud-based platform. This powerful solution enables IT departments to simultaneously monitor and manage multiple locations from a centralized interface. Organizations requiring data tracking for regulatory compliance will appreciate the built-in security auditing capabilities that support standards like HIPAA and PCI-DSS.
The platform excels in providing managed service providers with tools designed specifically for multi-client network oversight. Its compliance features help organizations maintain adherence to industry regulations while protecting personally identifiable information through dedicated tracking and security protocols.
Network administrators benefit from robust scanning functionality that identifies potential security vulnerabilities, including misconfigurations, unauthorized open ports, and system weaknesses. The comprehensive vulnerability assessment system categorizes security issues by severity, allowing teams to prioritize remediation efforts effectively.
As a cloud-based solution, N-Sight includes device discovery and inventory management across distributed environments. The integrated patch management system helps maintain current software and operating systems, effectively closing potential security gaps that could be exploited by malicious actors.
Security monitoring extends to both endpoints and network devices, providing comprehensive protection throughout the infrastructure. The remote monitoring and management tools include specialized assessments for PII exposure vulnerabilities, while usage analysis capabilities help identify potentially risky data handling patterns and emerging trends.
N-Sight: Comprehensive Network Security Solution
N-able N-Sight delivers robust security auditing capabilities through its integrated Risk Intelligence module. This sophisticated system identifies and monitors personally identifiable information (PII), providing essential oversight for organizations concerned with data protection compliance.
Security auditors will appreciate the specialized scanning tools that reveal inappropriate access permissions and generate detailed reports on potential data breaches. These features prove invaluable during compliance assessments and security reviews.
The platform extends beyond basic security with comprehensive endpoint protection, including advanced threat detection and response mechanisms. Its automated patch management ensures systems remain protected against known vulnerabilities, though this functionality primarily serves Windows environments.
Network defense is strengthened through integrated antivirus protection and firewall capabilities that safeguard both network infrastructure and connected devices. The system's backup and recovery functions provide additional protection against data loss incidents.
While N-Sight excels in Windows environments, its applicability to diverse operating systems is limited. The patch management specifically targets Windows systems, making it less optimal for networks incorporating Linux devices.
The cloud-based platform features customizable dashboards and reporting tools that provide tailored visibility into security metrics. Its multi-tenant architecture makes it particularly well-suited for managed service providers overseeing multiple client environments.
Organizations can evaluate N-Sight through a 14-day free trial, allowing risk-free assessment of its comprehensive security auditing capabilities, vulnerability scanning, compliance reporting, and centralized management features.
For enterprises requiring HIPAA, PCI-DSS, or GDPR compliance, N-Sight's built-in compliance templates streamline reporting processes. The real-time threat monitoring capabilities enable prompt incident response, enhancing overall security posture.
Available at www.n-able.com/products/n-sight-rmm/trial
Intruder.io is a cloud-based vulnerability scanning solution designed to help businesses identify and address potential security weaknesses in their networks. It provides both external and internal network scans, making it a comprehensive tool for enhancing network security.
The service offers several key features:
- Flexible Scanning Frequencies: Users can customize the frequency of their vulnerability scans according to their specific needs.
- Cloud-Based Accessibility: The platform is accessible from anywhere, providing convenience and ease of management.
- Extensive Vulnerability Database: The system covers over 9,000 known vulnerabilities, ensuring a thorough scan of your network.
- Visual Performance Metrics: Detailed, graphical reports help users understand their network's security status at a glance.
Upon signing up, Intruder.io performs a comprehensive initial scan of the entire system. This full vulnerability check is repeated monthly. Additionally, the service automatically triggers intermediate scans whenever new threats are added to its threat intelligence database. These intermediate scans focus on the specific hardware and software that may be vulnerable to the newly discovered exploits.
One of the key advantages of Intruder.io is its cloud-based nature. This allows the service to simulate the perspective of an external attacker, providing a realistic view of the network's security. The scans cover all aspects of the IT infrastructure, including on-site elements and cloud services. The system also detects common web application vulnerabilities, such as SQL injection and cross-site scripting, ensuring a robust defense against a wide range of potential threats.
Intruder, a network security auditing tool, employs an agent that needs to be installed on the network. This agent not only identifies external threats but also inspects for vulnerabilities from insider threats.
The service is subscription-based and offers three distinct plans: Essential , Pro , and Verified . The Essential plan provides an automatic monthly scan, while the Pro plan includes both the monthly scan and the ability to perform on-demand vulnerability scans. The top-tier Verified plan incorporates all the benefits of the Pro plan, plus the added expertise of a human penetration testing team.
This system is designed to cater to businesses of all sizes. The tiered pricing model makes it particularly appealing, with the Essential plan offering affordable monthly automated vulnerability scans. This is ideal for smaller businesses. On the other hand, the Verified plan, which includes the services of a human penetration testing team, is well-suited for large companies that need to meet strict data security compliance standards.
Intruder is a cloud-based solution, ensuring that its vulnerability database is always up-to-date. This means your system is continuously scanned for the latest security weaknesses, without the need for on-premise infrastructure.
Key features of Intruder include:
- Intuitive User Interface: Designed to be user-friendly and visually appealing, making navigation straightforward.
- Automated Vulnerability Detection: Automatically scans new devices and recommends necessary updates.
- Cloud-Hosted Convenience: No need for on-premise hardware, as everything is managed in the cloud.
- Web Application Vulnerability Assessment: Provides comprehensive testing for web-based vulnerabilities.
- Tiered Pricing Model: Offers flexible plans to accommodate businesses of various sizes.
- Complex Feature Exploration: While the system is powerful, fully understanding all functionalities may require some time.
- Limited Scan Frequency in Basic Plan: The Essential plan restricts scans to once a month, whereas the Pro and Verified plans offer more frequent and on-demand scanning options.
Scans are performed automatically every month with the Essential plan. For those who need more flexibility, on-demand scans are available with the Pro plan. Intruder also offers a 30-day free trial, allowing you to experience the service before committing.
Vulnerability Manager Plus by ManageEngine is a robust security solution designed to detect, document, and mitigate system vulnerabilities. It meticulously inspects both installed software and device configurations to pinpoint potential weaknesses that are commonly exploited by hackers. This comprehensive scanning process covers endpoints and network appliances, ensuring a thorough evaluation of the entire system.
The key features of Vulnerability Manager Plus include:
- System Configuration Analysis: Enhances security settings across all devices.
- Comprehensive Software Assessments: Conducts detailed examinations of installed software to identify any vulnerabilities.
- Updated Threat Intelligence: Regularly receives updates on emerging security threats to stay ahead of potential risks.
This toolset is an excellent choice for organizations looking to discover and manage all their assets, conduct vulnerability scans, and remediate identified exploits. The platform allows for the integration of exploit identification and resolution, enabling automatic fixes. Alternatively, you can choose to keep these processes separate, requiring manual intervention. The package comes in three different plans, with the top-tier plan including a patch manager and a configuration manager for effective remediation.
The vulnerability scan provided by this tool serves as a periodic security audit. It offers an automated system check that is more comprehensive than manual procedures. The scans are capable of evaluating devices running Windows, macOS, and Linux. The tool examines the operating systems of all connected devices and inspects all installed software. Additionally, it evaluates the settings of security tools like firewalls and audits web services and communication protocols to ensure there are no weak points.
Comprehensive Network Vulnerability Management Solutions
In today's cybersecurity landscape, proactive vulnerability assessment is essential for maintaining network integrity. Modern security auditing platforms offer automated vulnerability detection with regular scanning cycles—typically running every 1.5 hours—to ensure continuous protection.
Leading solutions integrate real-time threat intelligence feeds that automatically update when new vulnerabilities emerge. Upon detection of emerging threats, these systems immediately initiate targeted scans to identify potential exposure within your infrastructure.
Effective vulnerability management extends beyond mere detection to include automated remediation capabilities. Advanced platforms feature integrated patch management functionality that identifies necessary updates for both applications and operating systems, deploying them according to customizable schedules. Additionally, these tools provide actionable recommendations to address security gaps identified during vulnerability assessments.
Platform Requirements and Deployment Options
Most enterprise-grade vulnerability management solutions require Windows Server environments for controller deployment. However, they can effectively monitor endpoints across multiple operating systems including Windows, macOS, and various Linux distributions.
Key Features of Modern Vulnerability Management Tools:
• Scheduled vulnerability scanning with customizable frequencies
• Real-time threat intelligence integration
• Cross-platform endpoint monitoring capabilities
• Automated patch deployment functionality
• Prioritized remediation guidance
• Compliance reporting and documentation
Licensing options typically follow a tiered approach, with entry-level offerings supporting limited device counts—often around 25 nodes—making them suitable for small business environments. Mid-tier licenses generally support single-site deployments, while enterprise editions provide multi-site coverage across wide-area networks.
Most vendors offer free evaluation periods (typically 30 days) allowing organizations to assess functionality before committing to implementation. This approach enables security teams to verify compatibility with existing infrastructure and confirm that operational requirements are met.
Atera is a comprehensive platform designed to assist with the monitoring and management of remote systems. It offers a suite of tools that are particularly beneficial for managed service providers (MSPs) and IT departments. One notable feature within this platform is its reporting facility, which can generate a wide range of system audit reports.
- Designed for MSPs: Atera is specifically tailored to meet the needs of managed service providers.
- Flexible Pricing: The platform operates on a per-technician subscription model, allowing for cost-effective scaling.
- Security Auditing Reports: These detailed reports provide in-depth security analysis, enhancing overall system security.
The platform is available in versions suitable for both IT departments and MSPs. As a remote monitoring and management (RMM) system, it includes an integrated ticketing system, making it a complete solution for IT support teams, whether they are in-house or external. To ensure secure access, each technician must have their own account with unique credentials, which also enables the logging of their activities. This feature alone significantly enhances security auditing capabilities.
Atera maintains and updates hardware and software inventories, providing the foundation for an automated patch manager. This not only keeps systems up-to-date but also helps to document and enhance their security. When a new system is added to the platform, Atera’s server deploys an agent to the target network. This agent uses SNMP to gather information about the devices on the network, facilitating thorough and accurate monitoring.
Efficient network asset inventory management is crucial for maintaining a secure and well-organized system. With Atera, this inventory is continuously updated, forming the foundation for its automated monitoring capabilities. The tool operates by setting performance thresholds, which, when breached, trigger alerts to notify you of potential issues. For those requiring detailed network visualization, Atera offers a network mapping feature, though it comes at an additional cost.
Pricing for Atera is based on the number of technicians, making it a flexible solution for support teams of any size. Whether you're an independent freelancer or part of a large organization, the same comprehensive package is available. Being a SaaS solution, Atera can be accessed from anywhere, including from home, providing flexibility and convenience.
- Comprehensive Remote Monitoring: Quickly set up and monitor client networks with ease.
- Adaptable Reporting Tools: Generate tailored reports to meet various audit requirements.
- Asset Inventory Tracking: Keep track of all hardware and software in real-time.
- Network Discovery Updates: Regularly refreshes information on network devices.
- Limited Linux Support: No dedicated agent for Linux systems, which may be a drawback.
- Extra Cost for Network Mapping: Essential features like network mapping require an additional fee.
Atera is offered as a subscription service with three different plan levels, catering to businesses of all sizes. As a cloud-based platform, there's no need for on-site software installation. All data and performance records are securely stored on Atera’s servers. To evaluate if Atera meets your needs, you can start with a free trial.
ManageEngine Log360 is a comprehensive SIEM (Security Information and Event Management) solution designed to help organizations meet various compliance requirements. It supports standards such as HIPAA, PCI DSS, FISMA, SOX, GDPR, and GLBA by providing robust auditing and reporting features.
The system consists of a central server and multiple device agents. These agents are responsible for collecting log messages from different sources and sending them to the central server for processing.
Upon receiving the log messages, the Log Manager in Log360 standardizes the data into a common format. This consolidation ensures that the log records can be easily searched and analyzed for compliance purposes.
Key Features:
- Comprehensive Log Collection: Capable of gathering data from a broad range of sources, including network devices, operating systems, and software applications.
- Unified Log Management: Efficiently consolidates and organizes log data, making it easy to manage and search.
- Compliance-Driven Reporting: Generates reports tailored to specific compliance standards, ensuring that organizations can meet their regulatory requirements.
In addition to its core functionalities, ManageEngine Log360 includes a log manager that gathers, consolidates, and files log messages. These records are then available for automated security searches and manual ad-hoc data analysis. The system also tracks user activity and builds profiles of typical behavior for each account, enhancing its ability to detect anomalies and prevent data loss.
Log360 offers real-time dashboard monitoring of log messages with comprehensive data analysis capabilities. The system features robust search tools and pre-configured compliance reports that streamline security assessments.
The integrated Threat Hunter module leverages intelligence feeds to identify suspicious activities, generating immediate alerts that can be seamlessly routed through your existing service desk management system for prompt technician response.
Designed primarily for Windows Server environments, Log360 extends its log collection capabilities across multiple platforms including Linux and major cloud services like AWS and Azure. The package delivers extensive Active Directory analysis and enhancement features alongside its core log management functionality.
While particularly valuable for mid-sized to large organizations facing complex compliance requirements such as HIPAA, PCI DSS, FISMA, SOX, GDPR, and GLBA, the system's extensive feature set may prove unnecessarily robust for smaller businesses with simpler needs.
Key advantages include instant security incident notifications, powerful data examination tools, and automated compliance reporting. The solution effectively integrates threat intelligence to address emerging security challenges. However, potential users should consider its Windows Server platform requirement and the potential complexity for smaller deployments.
Organizations interested in exploring Log360's capabilities can access a comprehensive 30-day free trial through ManageEngine.
Site24x7: Comprehensive Network Security Monitoring Solution
Site24x7 delivers advanced network security auditing capabilities through its integrated monitoring platform. This cloud-based SaaS solution provides organizations with real-time visibility into their network security posture.
Core Security Capabilities:
Security Log Analysis
Site24x7 aggregates and processes security logs from diverse sources including firewalls, routers, servers, and intrusion detection systems. This comprehensive logging enables thorough security event monitoring across the entire network infrastructure.
Proactive Threat Detection
The platform excels at identifying suspicious activities, unauthorized access attempts, failed logins, and configuration changes that might indicate security breaches or vulnerabilities.
Real-Time Security Alerting
Administrators receive immediate notifications about potential security incidents, allowing for rapid response to emerging threats before they can cause significant damage.
Visual Security Intelligence
The solution features intuitive dashboards that present security metrics in easily digestible formats, enabling efficient data analysis and trend identification for security professionals.
Compliance Management
Organizations in regulated industries benefit from pre-configured compliance reporting templates that address requirements for PCI-DSS, HIPAA, GDPR, and other regulatory frameworks.
Network Configuration Management
The Network Configuration Manager component provides detailed oversight of device configurations, helping to maintain security standards and identify potential configuration vulnerabilities.
Business Benefits:
Scalable Security
The platform adapts to organizations of all sizes, from small businesses to large enterprises with complex network infrastructures.
Comprehensive Monitoring
Site24x7 combines multiple monitoring tools in a single solution, providing holistic visibility across network security, performance, and availability.
Regulatory Compliance Support
Automated reporting capabilities simplify audit processes and help maintain compliance with industry regulations.
Cloud-Based Convenience
As a SaaS platform, Site24x7 eliminates the need for on-premises hardware while providing flexible access to security monitoring capabilities.
Site24x7 is particularly valuable for businesses requiring robust security auditing in complex environments and those in highly regulated industries like healthcare, finance, and e-commerce. New users can evaluate the platform through a 30-day free trial period.
Netwrix Auditor: Comprehensive Network Monitoring Solution
Netwrix Auditor provides robust configuration change monitoring capabilities within your network environment. The intuitive dashboard displays detailed system modification information, capturing critical elements such as the action performed, the responsible party, affected resources, timestamp, and location. This comprehensive approach ensures complete visibility into all network changes.
Core Capabilities
The platform excels at tracking user access patterns, generating detailed security audit documentation, and implementing automated security measures to protect network configurations. Its continuous operation mode effectively transforms it into a real-time intrusion detection system.
Security Monitoring Functions
The solution thoroughly examines network devices with particular attention to:
• User account management
• Permission level verification
• Insecure access protocols
• Authentication attempts
• Configuration alterations
Real-time alerting notifies administrators of potential vulnerabilities while simultaneously maintaining detailed logs for compliance purposes and reporting requirements.
Visual Security Intelligence
The interface clearly highlights security concerns with visual indicators—failed login attempts appear in prominent red boxes for immediate identification of potential breach attempts. Additionally, the system monitors critical hardware metrics including processor temperature, power systems, and cooling components.
Automated Incident Response
Netwrix Auditor features a sophisticated alert system with scripting capabilities. When security events occur, the platform can automatically execute predefined scripts, such as generating help desk tickets to initiate remediation workflows.
Microsoft Environment Focus
The solution is particularly well-suited for Microsoft-centric infrastructures, making it less ideal for Linux-based environments. Small businesses may benefit from the available free Community Edition, while organizations requiring more comprehensive insights can upgrade to paid versions.
Additional Benefits
• Enhanced file security through comprehensive tracking
• Proactive hardware health monitoring
• Automated security response mechanisms
• Streamlined incident management
• API integration capabilities
For organizations seeking automated network security auditing with detailed event analysis, Netwrix Auditor represents a leading solution in the market. A 20-day trial version is available for evaluation before purchase.
Vulnerability Assessment Tools Overview
Enhancing Network Security: Essential Vulnerability Assessment Tools
In today's rapidly evolving cybersecurity landscape, organizations need reliable tools to identify and address potential vulnerabilities. Among the most effective solutions available is a comprehensive vulnerability assessment platform that offers both free and premium options.
This versatile security tool provides robust vulnerability scanning capabilities, allowing security professionals to conduct thorough network audits. The system can identify potential security gaps across configuration settings, missing patches, and various other vulnerability types.
One of the tool's most valuable features is its rapid response to emerging threats. With new vulnerability detection plugins typically released within 24 hours of discovery, and automatic updates ensuring these capabilities are immediately available, organizations can stay ahead of evolving cyber threats.
The platform excels in several key areas:
• Extensive vulnerability database covering more than 50,000 known security issues
• Risk-based categorization system that helps prioritize remediation efforts
• Configuration assessment capabilities
• Patch management functionality
While originally developed as an open-source project, the current proprietary version maintains a free tier that supports scanning up to 16 IP addresses - making it accessible for smaller environments or initial testing. For larger networks, premium versions offer expanded functionality and unlimited scanning capabilities.
The detailed reporting system categorizes findings by severity level, enabling security teams to address the most critical vulnerabilities first while developing comprehensive remediation plans.
Nessus offers over 450 configuration templates, making it exceptionally user-friendly for security professionals. These templates cover everything from basic network scans to specialized assessments targeting specific threats like WannaCry ransomware.
The reporting capabilities are particularly robust, allowing users to generate customized reports that categorize vulnerabilities by severity levels (critical, high, medium, low, and info). These reports can be exported in multiple formats including HTML, CSV, and XML for easy sharing among team members.
While Nessus is primarily designed for medium to large organizations, smaller businesses can benefit from Nessus Essentials at no cost. Security professionals should note that OpenVAS represents a free alternative, having been forked from Nessus when the latter transitioned to a commercial model.
Among Nessus's strengths are its frequent plugin updates that address emerging threats, an intuitive interface, and flexible reporting options. However, potential users should consider some drawbacks: resource-heavy scanning processes that may affect performance, limited compatibility with certain security tools, and premium pricing for enterprise-level features.
For those interested in comprehensive vulnerability assessment, Nessus Professional offers unlimited IP scanning starting at approximately $2,990 annually. A 7-day trial is available for evaluation purposes, while the free Essentials version supports scanning up to 16 IP addresses.
The Trellix XDR platform is a cloud-based, comprehensive security solution that integrates both endpoint and network monitoring. This system ensures robust protection by not only tracking device-level activities but also by monitoring the broader network for signs of intrusion or malicious activity.
At its core, the Trellix XDR package includes an NDR (Network Detection and Response) component, which complements the endpoint monitoring service. While the endpoint monitor focuses on detecting unusual behavior on individual devices, the NDR is designed to identify and thwart lateral movement attempts. Lateral movement is a common tactic used by malware to propagate across an organization's network, making this feature crucial for preventing widespread infection.
Key features of the Trellix XDR platform include:
- Lateral Movement Detection: This feature identifies and blocks the spread of malware as it moves from one device to another, ensuring that a single compromised endpoint does not lead to a full-scale breach.
- Anomalous Access Identification: The system flags any unexpected or unauthorized access attempts, helping to prevent potential breaches before they can cause significant damage.
- Comprehensive Threat Mitigation: Once a threat is detected, the Trellix XDR platform responds swiftly to neutralize it, minimizing the impact on the network and the organization.
The platform operates by deploying agents on-site, which work in tandem with the cloud-hosted management console. This combination of endpoint and network monitoring provides a multi-layered defense strategy. By focusing on hosts, where all executables run, the tool excels at detecting and isolating malware and intruders. The NDR feature plays a critical role in this process by blocking all traffic originating from infected devices, effectively containing the threat and preventing it from spreading further.
In scenarios where a user account is compromised or malware infects a single endpoint, the Trellix XDR platform's automated responses are instrumental in preventing the situation from escalating. For example, if an attacker tries to use a stolen account to access sensitive data on other devices or if ransomware begins to spread across the network, the platform's rapid response capabilities help to mitigate these threats, ensuring that the organization remains secure.
Trellix System's comprehensive security logging capabilities serve a dual purpose: enabling thorough forensic analysis of security events and supporting compliance documentation requirements. This functionality is particularly crucial for organizations handling confidential information that must adhere to strict regulatory frameworks.
The cybersecurity landscape constantly evolves with emerging attack vectors. No security solution can anticipate every possible threat signature. This reality underscores the critical importance of Network Detection and Response (NDR) systems, which provide essential protection by restricting unauthorized network movement regardless of the attacker's specific techniques.
Data protection is a universal business necessity. Proactive security measures deliver superior outcomes compared to reactive approaches. NDR technologies exemplify this preventative philosophy by acknowledging that any seemingly insignificant network endpoint can become a security liability through user error. Effective security architecture must prevent lateral movement from compromised devices to critical data repositories.
Key considerations include:
Cloud-based deployment offering operational flexibility and remote accessibility
Integrated protection covering both endpoint devices and network infrastructure
Automated compliance documentation through systematic log management
Continuous internet connectivity requirement for full functionality
For a practical demonstration of Trellix XDR capabilities, demonstration sessions are available upon request.
Network Security Exploration with Nmap
Nmap stands as one of the most powerful network reconnaissance tools available today. This versatile port scanner enables security professionals to discover hosts and identify potential vulnerabilities across networks.
Capabilities Overview
Nmap provides detailed port status information through its command-line interface, classifying ports as open, closed, or filtered. The tool goes beyond basic scanning by revealing crucial details including service versions and operating system information, helping administrators identify systems requiring security patches.
Interface Options
While primarily operating through a command-line interface that offers precise control, users seeking a more intuitive experience can utilize Zenmap, the graphical companion to Nmap. Zenmap enhances usability while maintaining Nmap's powerful scanning capabilities and adds network visualization features.
Advanced Functionality
Security professionals appreciate Nmap's scripting capabilities through Lua, enabling automated scanning routines that save significant time during security assessments. These automation features allow for consistent, scheduled security checks without manual intervention.
User Base and Accessibility
The tool serves diverse users including network administrators, penetration testers, and security researchers. Its free availability and cross-platform support (Linux, Windows, Unix, and FreeBSD) make it accessible to organizations of all sizes.
Considerations
While powerful, Nmap presents a learning curve that may challenge beginners. The core tool lacks built-in visualization, requiring Zenmap for graphical representation. Additionally, Nmap focuses on point-in-time scanning rather than continuous protection, making it one component of a comprehensive security strategy rather than a complete solution.